Axios and npm are important.
A lot of web development tools and services use many different technologies. Axios is a popular JavaScript HTTP client that uses promises. With Axios, developers can handle requests for web frontend apps, backend services, and development pipelines. There are an average of 100 million downloads from the npm registry per week. Its simplicity and adaptability make it a popular choice across various fields.
npm is the default tool for keeping Node.js's JavaScript ecosystem in excellent shape. This tool speeds up development and comes up with new ideas about how to make the code easier to share and reuse. It can be dangerous to be simplistic. Because of many dependencies, a bug in one popular package can disrupt millions of programs. NPM accounts and packages work together; thus, they need to be safe. The most recent security issue with the npm Axios package highlights how unsafe our software supply chain is.
A look back at the Axios Supply Chain Incident from March 2026
On March 31, 2026, a sophisticated attack against the Axios npm package's supply chain occurred. The attack shocked software developers. The npm Axios security hole let bad libraries be downloaded while the program was executing. Developers, build systems, and production environments were all in jeopardy.
From 00:21 to 03:30 UTC on March 31, 2026, npm sent out bad packages. During this short but important time, two hacked versions of Axios were made available: axios@1.14.1 ("latest") and axios@0.30.4 ("legacy"). The ecology was most vulnerable when both new and old branches were attacked at the same time.
When npm administration found the fake packages, they swiftly took them from the registry. Scientists say it quickly expanded to 3% of the affected areas. It highlighted how weak the software supply chain is and what occurs when a big library is taken over.
Supply chain disruptions like this one share patterns with large-scale infrastructure failures seen in other sectors. Just as developers rely on npm packages, businesses depend on cloud platforms for core communication — when those fail, the damage spreads fast, similar to what happened during the Microsoft Outlook and Microsoft 365 outage in the US.
Malware and a compromise at Axios
Threats on npm, Axios shows off skills. There are numerous steps in an assault chain:
Violation of the Maintainer Account
Jason Sayman, the project manager for Axios, lost his npm account. Hackers releasing updated versions of the real Axios package was a very important first step. The hacker modified the email address to ifstap@proton.me. This made it hard for the person who had the account to get in and get it back.
Bad Dependency Precursor
Eighteen hours before the attack, the attacker made plain-crypto-js@4.2.0, a "decoy" package. This version was uploaded to a temporary npm account with a short, believable registry history so that it wouldn't be noticed. This showed that the person was smart and had planned ahead instead of taking advantage of others.
Add a bad load
Hackers introduced the harmful dependency plain-crypto-js@4.2.1 to the package.json files for Axios 1.14.1 and 0.30. 4. The attackers didn't change. Axios' source code, which is the most crucial thing. This makes it straightforward to check. This attack was possible because of plain-crypto.js-js.
After you install the broken plain-crypto-js@4.2.1 package, the script starts.json. After you install npm or Bun, run this script. Run the script to drop a RAT that worked on every system. GTI found out about WAVESHAPER. V2 was a RAT that sent payloads to Windows, macOS, and Linux.
Stay away from CI/CD and anti-forensics.
The attackers used stolen maintainer credentials to publish bogus versions using the npm CLI. Branch safeguards and code review gates in GitHub Actions normally stop unauthorized changes, but not this time. The bad versions were on npm, not on Axios' git tags, commits, or release branches.
To finish the forensics, the RAT dropper was cleaned. It ran the JSON, erased itself, and then put the package back. The trigger for node_modules postinstall was taken out. This complicated adjustment was meant to make it harder to find and look at evidence.
Finding Attacks on the Supply Chain
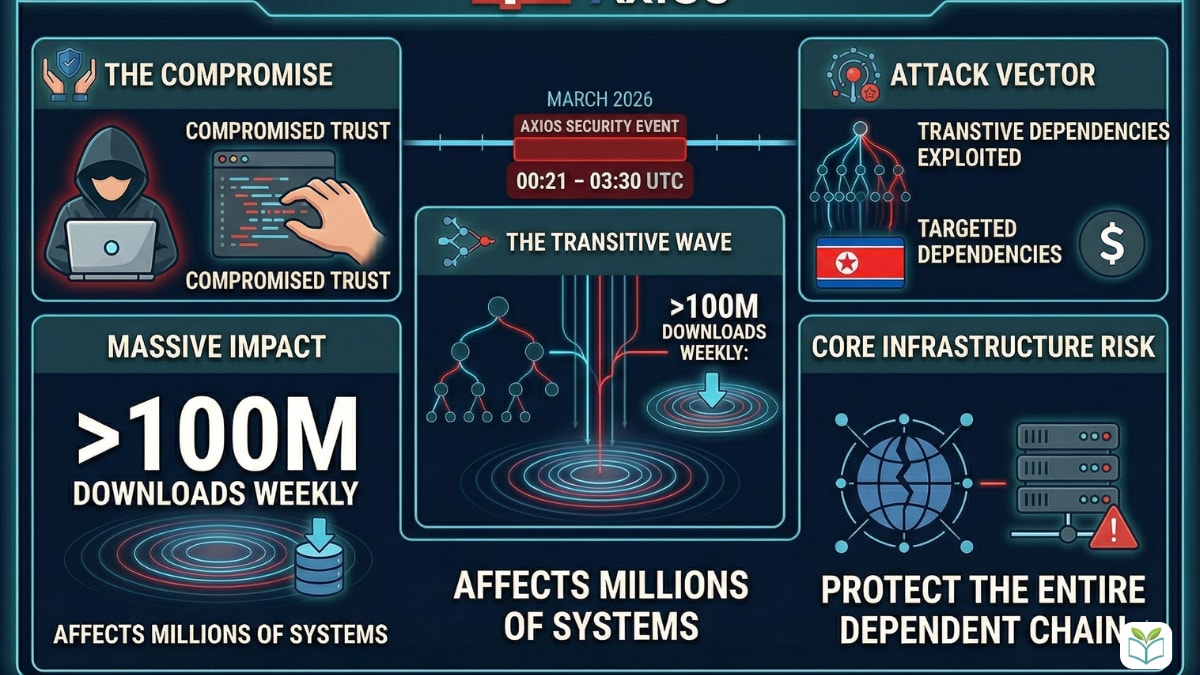
Attacks on the computer supply chain, like the npm Axios security event, are on the rise. Attackers go at flaws in software, not the gadgets of users. Someone can hack a trusted open-source library and send it to all the programs and systems that use it.
It has a lot of crucial effects:
Using Faith: The attack took advantage of developers' faith in well-known open-source software. Hacking Axios breaks the faith in the ecosystem.
This breach might be a big deal because millions of apps use Axios and more than 100 million people download it every week. Another package may add broken versions that affect systems that don't use Axios as a transitive dependency.
The sophisticated attack was hard to find because of pre-staging, CI/CD circumvention, and anti-forensics. Standard code reviews didn't catch hazardous code that depended on Axios.
GTIG says that the North Korean hacker UNC1069 uses the WAVESHAPER.V2 backdoor and wants money. These attacks are probably the work of rich, government-backed, or smart groups. Analyst: "The attack surface is the vendor's vendor's vendor." In real life, it looks like this. Businesses need to protect their code, its dependencies, and the dependents of those dependencies.
The npm Axios leak shows how complicated and fragile the software distribution chain is. It needs to be watched and protected at all times. Security filters that catch threats at the pipeline level — much like Gmail filters that stop working and miss threats — are a reminder that detection tools are only as good as their configuration and maintenance.
Fixing the breach now
The npm Axios security problem hurt both businesses and developers, who need to act right away. If someone hacked Axios, assume that your information was stolen and take action.
Do them right away:
From 00:21 to 03:30 UTC on March 31, 2026, dangerous versions were available. It's dangerous to use npm install today.
Look at your dependencies and lockfiles:
Look in your package-lock.json (or Yarn/pnpm lockfiles) for direct or indirect dependencies on axios@1.14.1, 0.30.4, or the unsafe plain-crypto-js@4.2.1.
These versions could all be bad for your system.
Separate the systems that are affected right away:
Bad versions on a development workstation, a CI/CD pipeline, or a production server must be removed right away. This prohibits criminals from getting into your infrastructure.
Think of your tools as broken and mend them:
Don't do remediation in place. The dropper is anti-forensics, so regular cleanups might not find everything.
By March 30, 2026, you need to re-image or restore affected equipment using a clean backup.
Change all of your passwords:
Get back and reissue all the hacked system credentials. Instead of rotating, act like they're damaged and worthless. This includes:
- To get in, use npm tokens.
- IAM roles and credentials for Azure, GCP, and AWS.
- Bitbucket, SSH, GitLab, and GitHub.
- Secrets for Jenkins, CircleCI, and GitHub Actions.
- How to get to the database.
Review of the IOC and the downturn:
Look through your network logs for C2 connections that came from this assault. Look at the traffic on sfrclak.com or 142.11.206.73.
The RAT gave the hacker the ability to run any code, move sideways, list systems, and steal information. Look for things that aren't normal.
CI/CD deployments are over:
Do not deploy packages and projects that depend on Axios until you have finished assessing and reducing the risks.
Talk about and write down:
Tell the right people at the company about the possible breach and what they need to do next. Write down your answers and learn from them.
After the Axios security breach, quick action is needed to limit the damage and stop future attacks.
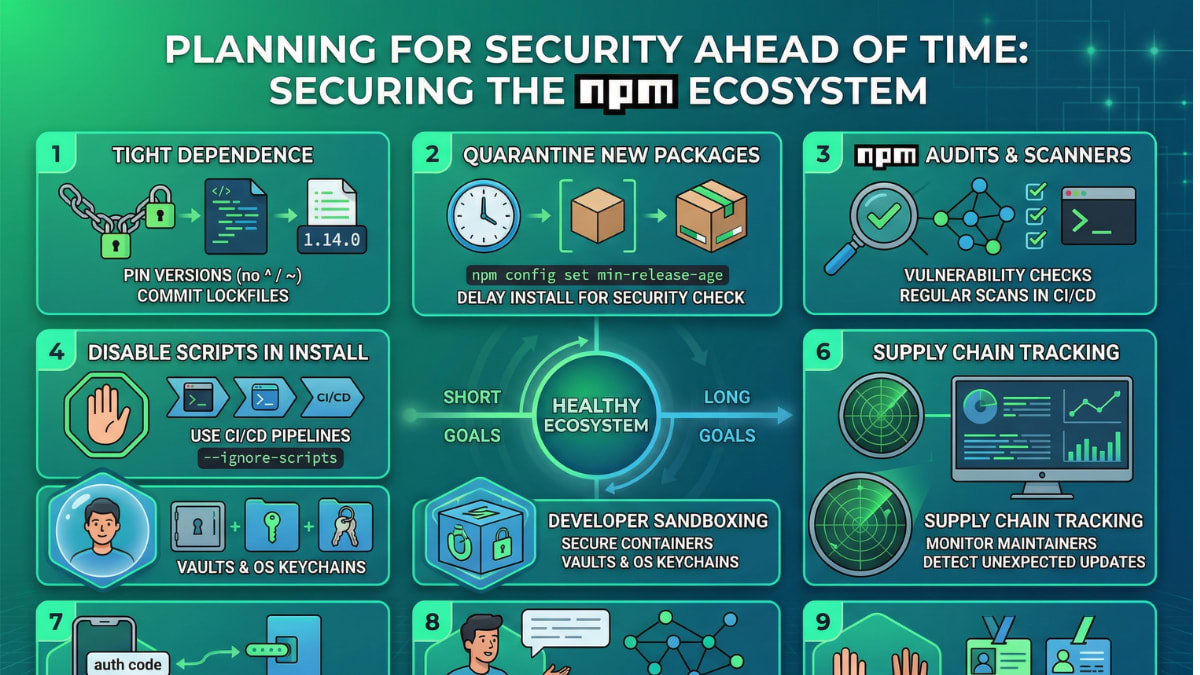
Planning for security ahead of time
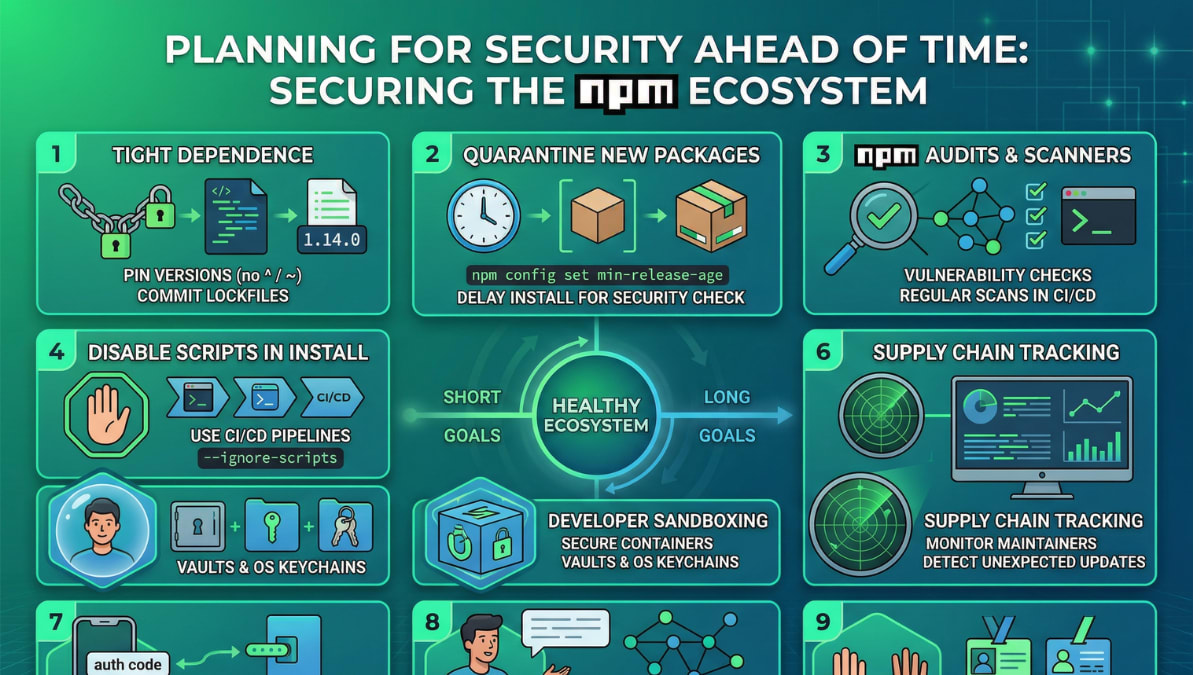
npm users should make their systems safer after the Axios incident. For a healthy software ecosystem, there need to be both short-term and long-term goals.
npm users have a lot of options for keeping themselves safe:
Tight Dependence:
Packed. In JSON, pin dependencies to versions that are known to work. Put package-lock.json or yarn.lock/pnpm-lock.yaml in version control. You won't accidentally install updates that are bad for you. Don't use big version ranges like ^1.14.0 for minor or patch upgrades, as the Axios exploit showed.
Put new package versions in quarantine for a short time:
To put off installing a package, run npm config set min-release-age <hours>. npm config set min-release-age 72 will take 72 hours to install so that security scanners and the community can find and report dangerous packages.
Use npm audits and vulnerability scanners.
Use npm audit to check your dependencies for security holes on a regular basis. In CI/CD, use this to find problems early.
Security tools from other companies can find dependencies and break apart software.
Don't use scripts; utilize CI/CD instead.
For npm install, CI/CD pipelines should use --ignore-scripts. This lets the Axios RAT in by pausing preinstall, postinstall, and other processes that happen during the lifecycle. This might hurt real packages that require these hooks, but it stops evil scripts from getting in. How will it affect what you need?
Developer sandboxing and keeping secrets safe:
Containers or sandboxes stop developers from getting to the host filesystem. Developers' machines are less likely to be affected by bad packages.
Use OS keychains or hidden vaults like HashiCorp Vault or aws-vault to keep your API keys and cloud credentials safe. This stops malware from getting into host PCs and stealing logins.
Better tracking of the supply chain:
Use technology and best practices to keep an eye on your software supply chain at all times. Keep an eye out for new maintainers, package information updates that you didn't expect, and publishing actions.
Just as emerging AI tools like Google Veo 3.1 reshape how content pipelines are built, the development ecosystem must evolve its security practices to match the pace of innovation.
MFA for npm accounts:
Adding MFA to all npm accounts is a good idea, especially for package maintainers who are important. A hacked maintenance account started the Axios attack. MFA protects accounts by making it tougher to get into them.
Study Dependencies:
Let developers work on more things. Not all transitive dependencies can do this, but knowing who is in charge of direct dependencies and how they work may help you find problems.
Least Privilege:
Least privilege should be used to build and deliver all systems. Only give CI/CD pipelines and deployment agents the permissions they need.
By doing these things ahead of time, npm users may make their development process safer and less likely to be attacked through the supply chain.
Questions and Answers
What occurred with the npm Axios security issue?
On March 31, 2026, hackers got into the npm registry and put out fake Axios JavaScript HTTP clients. People who need secrets have a Remote Access Trojan (RAT) on their PCs.
Question 2: What problems do different versions of Axios have?
A2: 1.14.1 and 0.30.4 Axios is bad.
Q3: How long does it take you to download bad npm packages?
From 00:21 until 03:30 UTC on March 31, 2026, npm had broken versions. Someone saw them and took them.
Q4: What was the bad payload of the attack?
A4: The attack made a RAT that works on several platforms. The RAT utilized plain-crypto-js@4.2.1, which is a bad dependency.
What did hackers do to hurt Axios?
A5: Hackers got into the npm account of Axios's main maintainer, jasonsaayman. People that used stolen credentials put out bad versions of npm to get around CI/CD limits.
Q6: Who did the attack?
GTIG says that this operation is connected to the North Korean hacker UNC1069, who is doing it for money.
Can I check my systems for issues?
Look in package-lock.json for axios@1.14.1, 0.30.4, or plain-crypto-js@4.2.1. Look at the npm install logs from March 31, 2026, between 00:21 and 03:30 UTC.
What if my system breaks?
The machine that became infected should be kept separate and treated as if it were broken. Reimage or restore from a clean backup by March 30, 2026. Change the passwords on all the PCs that were affected.
Q9: Is it possible to stop attacks?
A9: Strict dependency pinning, a short quarantine on new packages (npm config set min-release-age), CI/CD --ignore-scripts, MFA for npm accounts, sandbox development environments, and regular dependency checks.
Finding out how strong the software ecosystem is
The npm Axios security event in March 2026 taught software developers a scary but important lesson. It highlights how bad things can get when a big part of the supply chain is hacked and how far hacking has come. The experience indicates that trusted libraries can be abused and that software development is getting increasingly connected.
npm and the security community immediately got rid of harmful packages, which helped limit the damage. Even though the vulnerability window was short, it affected a lot of computers. It's really important to protect yourself ahead of time.
We need to do a lot of things to keep the software ecosystem going:
Developers and businesses need to secure dependencies, from direct packages to the transitive graph.
We need security mechanisms like dependency pinning, multiple maintainer user IDs, and sandboxing development environments.
Use automatic security tools like vulnerability scanning, software composition analysis, and supply chain monitoring to find and fix problems rapidly.
Collaboration: Security experts, suppliers, and the open-source community immediately shared information and reacted to the Axios occurrence, showing how they might work together to protect themselves. To avoid new threats, people need to talk to each other and share information.
After the npm Axios problem, everyone needs to protect the software supply chain. Using security measures and learning from this experience can make software development safer and more reliable.